The search engine Ask.com leaked its server log files, displaying all of its users’ aearch queries to the public. For a few hours today, you searched for a keyword on Ask.com, the public could see what you searched for.
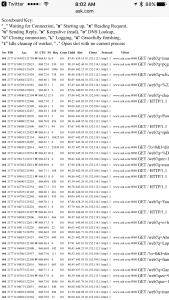
If went to this URL here: http://ask.com/server-status
you could see the server status, and the log file. A refresh of the page would reveal the latest search queries at the search engine.
Notice that the ask.com URL is NOT HTTPs. In contrast, Google for several years has been secure, not even allowing site owners to see search queries.
One of the search queries I saw on the log file was “blue monster speakers sams club”.
This would be a way that someone could scrape the file and get a list of keywords the publicity is using. As you might recall, years ago there was a similar day at breach at AOL that also allowed the public to see search query data.
This post has been updated from the original. According to CNet (https://www.cnet.com/news/ask-com-server-log-leak-is-showing-your-searches/) they got the following statement from Ask:
“We have been working to address the inadvertent publishing of the Ask.com server status page and can report that this matter has now been globally resolved,” said an Ask spokesperson. “We can confirm user IP addresses were not accessible during this incident, only queries and the IP addresses of our internal servers. We regret this error and are committed to protecting the confidentiality and security of our users’ information.”
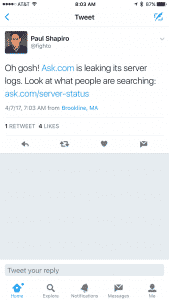
HT goes out to Paul, @fighto on Twitter, for alerting me to this.